Google’s new Confidential Virtual Machines on 2nd Gen AMD EPYC
by Dr. Ian Cutress on July 14, 2020 8:00 AM EST- Posted in
- CPUs
- Virtualization
- AMD
- EPYC
- Cloud
- Rome
- Containers

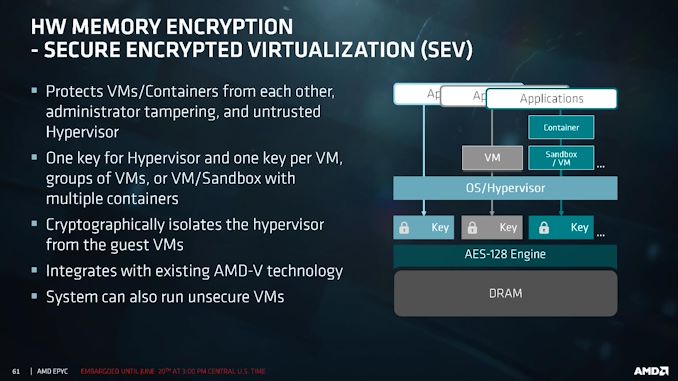
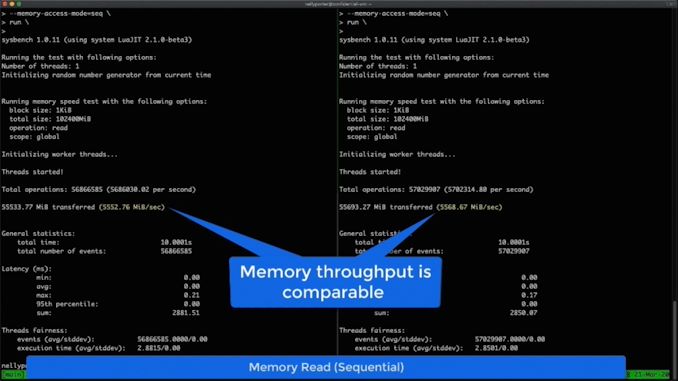
With AMD’s market share slowly increasing, it becomes very interesting to see where EPYC is being deployed. The latest announcement today comes from AMD and Google, with news that Google’s Compute Engine will start to offer new Confidential Virtual Machines (cVMs) built upon AMD’s Secure Encryption Virtualization (SEV) feature. These new cVMs are variants of Google’s N2D series offerings, and Google states that enabling SEV for full memory and virtualization encryption has a near zero performance penalty.
Secure Encryption Virtualization in AMD’s 2nd Gen EPYC processors allows cloud providers to encrypt all the data and memory of a virtual machine at the per-VM level. These are generated on-the-fly in hardware, and are non-exportable, reducing the risk of side attacks by potentially aggressive neighbors. Previously this sort of computing model was only possible if a host assumed control of a whole server, which for most use cases isn’t practical.
With SEV2, technically AMD allows for up to 509 keys per system. Google will offer images for its cVMs with Ubuntu 18.04/20.04, COS v81, and RHEL 8.2; other operating system images will be available in due course.
These cVMs will be available in vCPU listings, confirming that simultaneous multi-threading is enabled on the hardware. Both Google and AMD declined to comment on the exact EPYC CPUs being used, only that they were part of the 2nd Gen Rome family.
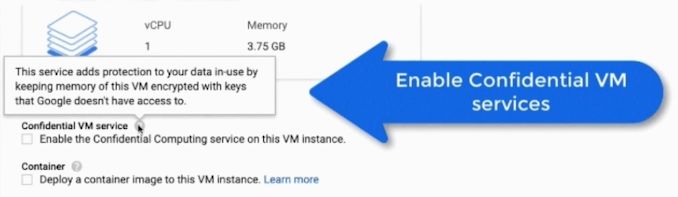
This is technically a beta launch, with Google being the first cloud provider to offer SEV-enabled VMs. Google is also promoting the use of its Asylo open-source framework for confidential computing, promising to make deployment easy at a high performance.
A number of 30 MB gifs were created by Google to showcase the new cVMs. Rather than share them with you in an outdated 1989 format, we converted them to video:
Users wanting access to the new VMs should go to the relevant Google page.














20 Comments
View All Comments
edzieba - Tuesday, July 14, 2020 - link
"I can't wait until AVIF(S) is a widely supported thing."Don't make me link that XKCD comic!
brucethemoose - Tuesday, July 14, 2020 - link
Indeed...Its the best shot so far, but I guess thats true of the whole gif replacement graveyard.
peevee - Tuesday, July 14, 2020 - link
Please do. 14-15?brucethemoose - Tuesday, July 14, 2020 - link
https://xkcd.com/927/PeachNCream - Tuesday, July 14, 2020 - link
Google is a technologically advanced company on the bleeding edge of - well mostly just on the bleeding edge of baiting people into using their services in order to run a profiling and advertising venture. No one ever said they had a clue how to use anything more modern than a sh*tty set of GIF images (eyes YouTube and then shrugs).SirPerro - Monday, July 27, 2020 - link
I hope you are kidding. Google is indeed technologically advance on the bleeding edge. Sometimes almost magically so.Brane2 - Tuesday, July 14, 2020 - link
Key phrase being "reducing the risk".IIRC an exploit has been published.
Brane2 - Tuesday, July 14, 2020 - link
Ofcourse obligatory backdoors are still secret.Deicidium369 - Tuesday, July 14, 2020 - link
All the Intel "vulnerabilities" are only achievable in the lab - would likely be the same with the AMD "vulnerabilities". Neither have any attacks in the wild - none are actually exploitable. Even in the lab the attacks were hit or miss.AMD are niche at best - so just like for the longest time there were very few Mac exploits - because they weren't worth the time. You put any tech under enough scrutiny and you will find all kinds of holes. This reminds me of Van Eck devices - being able to read CRTs at a distance - very interesting but ultimately not really usable.
Isn't Rowhammer still a thing on both Intel and AMD?
PeachNCream - Tuesday, July 14, 2020 - link
You must not be aware that this only provides temporary relief for your symptoms.